Cybersecurity
Infrastructure Protection: End Devices, Vulnerabilities, Data, Network Perimeter
About directions
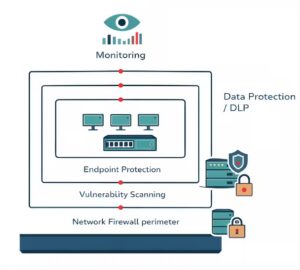
We implement solutions to protect IT infrastructure: vulnerability scanning, workstation and server protection, mobile device control, data leak prevention, firewall configuration.
Classic antivirus doesn't see targeted attacks, zero-day threats, and employee-caused leaks. Modern protection requires a complex approach: identifying vulnerabilities before an attack, monitoring system behavior, and controlling data at all levels.
In 2024, the Georgian Law on Personal Data Protection came into force, which made cybersecurity not a choice, but a legal necessity for companies working with personal data.
Decisions

- Vulnerability Scanning and Security Audit (Tenable)
- Endpoint Protection with Artificial Intelligence (SentinelOne)
- Mobile Device and Laptop Management (BlackBerry UEM)
- Data Loss Prevention and Information Classification (Fortra)
- Cross-network screen configuration and administration
- Network segmentation and access control
Technology partner — international distributor BAKOTECH. This provides the possibility of solution testing (PoC), training, and technical support.
For what tasks
- Antivirus and targeted attack protection
- Discover vulnerabilities before the bad guys do
- Employee device control (BYOD, corporate laptops)
- Data Loss Prevention (DLP)
- Compliance with the 2024 requirements of the Law of Georgia on Personal Data Protection
- Building a secure network perimeter
How I work
Starting with audit. We scan the infrastructure, identify vulnerabilities, and assess risks. You receive a report with a prioritized list of issues. According to Innocom's practice, even a basic scan reveals critical vulnerabilities in 80% of infrastructure that has not been audited.
We select solutions based on tasks and budget. We don't sell "everything at once," but first and foremost, we close critical risks.
We help with operation. We train staff, regulate notifications, and take action when necessary ტექნიკურ თანხლებას.
Related Services
Cybersecurity works with properly configured Network equipment and protected and protected Together.
For comprehensive protection, we recommend considering IT-outsourcing Through regular system monitoring and updates.
Let's consider the problem →
Describe what needs to be done, we will offer a solution and tell you the deadlines.
Frequently Asked Questions
Yes. The new version of the law (2024) imposes strict requirements on data storage and processing. We are conducting an audit and implementing technical means (encryption, access control, perimeter protection) to ensure that your business fully complies with the legislation.
We implement complex protection: from advanced Endpoint Detection and Response (EDR) systems to a data backup strategy that cannot be breached from the outside.
Email us
From technical task to working system
We create IT infrastructure for the real needs of your business, not according to templates. System design, installation, and configuration where reliability and thoughtful architecture are important.
Contact us
Let's consider the problem Describe your requirements and we will prepare a solution for your facility.
